Some options to beef up security on your Windows computer aren’t available in the Settings app. You can find them in the Group Policy Editor, provided you’re using Windows Pro or Enterprise editions. Let’s look at several of them.
To access the Group Policy Editor, press Windows+R to open the Run dialog box. Enter
gpedit.msc
in the text and click the “OK” button.
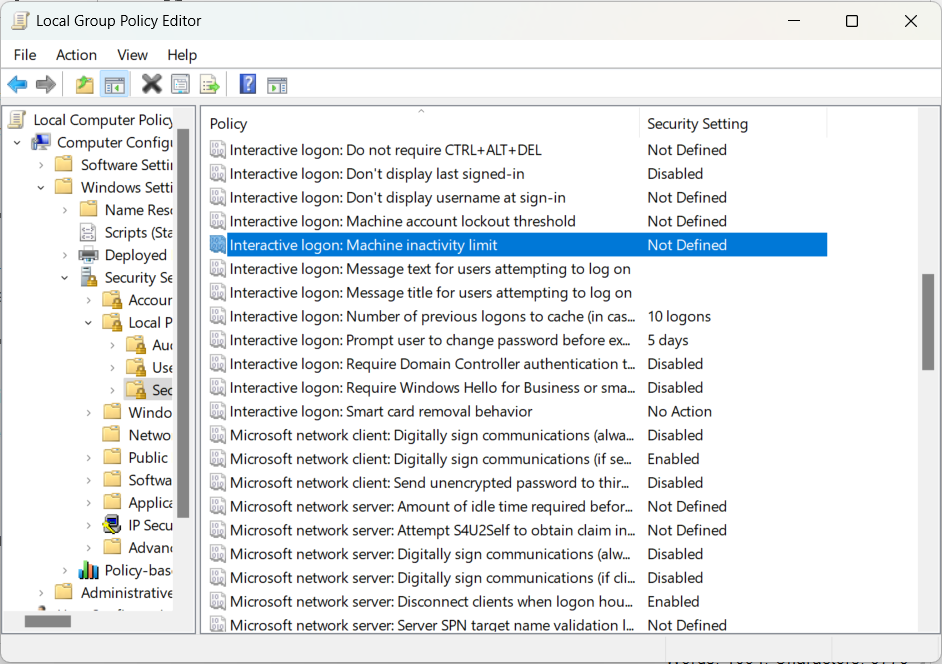
1 Screen Lockout Time
Enabling the screen lockout policy locks your computer after a specified period of inactivity. Using the computer after being locked out will require authentication, protecting your computer from unauthorized access.
To find the screen lockout policy in the Group Policy Editor, go to Computer Configuration > Windows Settings > Security Settings > Local Policies > Security Options. Here, edit the “Interactive Logon: Machine Inactivity Limit” policy.
You will need to enter the number of seconds that should pass before your computer automatically locks. You can pick a number between 0 and 599,940.
2 Password Policies
The default password policies on Windows are not that strict. For instance, users can use the same password indefinitely and don’t need to create complex passwords. Luckily, you can make them stricter by editing the right security policies.
To find the password policies in the Group Policy Editor, go to Computer Configuration > Windows Settings > Security Settings > Account Policies > Password Policy.
There are several group policies to tweak here. Here are the ones I recommend changing:
|
Password Policy |
Description |
Recommended Value |
|---|---|---|
|
Enforce password history |
Prevents users from repeating passwords. |
24 password remembers |
|
Maximum password age |
Forces users to change their password after a specified number of days. |
60-90 days |
|
Minimum password age |
Sets the number of days a user must wait before they can change their password since they last changed it. |
1 day |
|
Minimum password length |
Sets the minimum number of characters a user can enter when creating a password for their account. |
8-12 characters |
|
Password must meet complexity requirements |
Password should contain uppercase letters, lowercase letters, numbers, and special characters to be valid. |
Enabled |
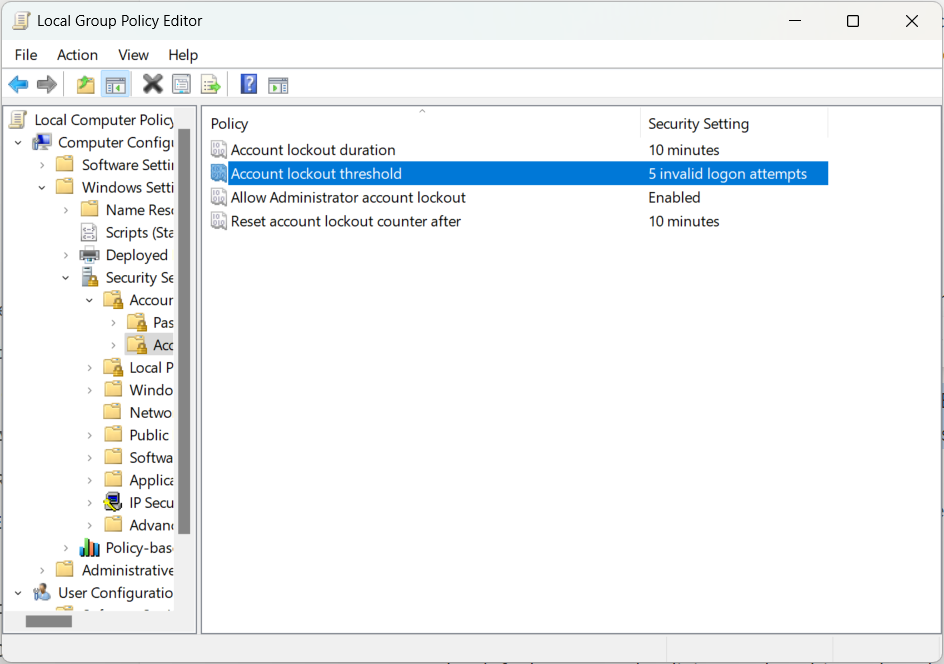
3 Account Lockout Threshold
If someone tries to hack into a user’s profile, they might try to guess the password. By setting the “Account Lockout Threshold” policy, you can ensure the account is locked for several minutes before the user can attempt to log in again or until an administrator unlocks it.
To find the “Account Lockout Threshold” policy in the Group Policy Editor, go to Computer Configuration > Windows Settings > Security Settings > Account Policies > Account Lockout Policy.
I’d recommend setting it to 3–5 login attempts before the account lockout period is triggered. Doing this will also enable the “Allow Administrator Lockout” policy and set the “Account Lockout Duration” and “Reset Account Lockout Counter After” policies to 10 minutes. You can tweak them individually if you want to if the default values don’t work for you.
Disabling removable media ensures flash drives, external drives, and other storage devices cannot be accessed on your Windows computer. That means no one can copy data from your computer or infect it with malicious software through these devices.
To disable removable media, navigate to Computer Configuration > Administrative Templates > System > Removable Storage Access. Find the “All Removable Storage classes: Deny All Access” policy and enable it.
If you want to set it for a specific profile instead of the whole computer, log into that profile, and enable the policy there. You will find it by going to User Configuration > Administrative Templates > System > Removable Storage Access.
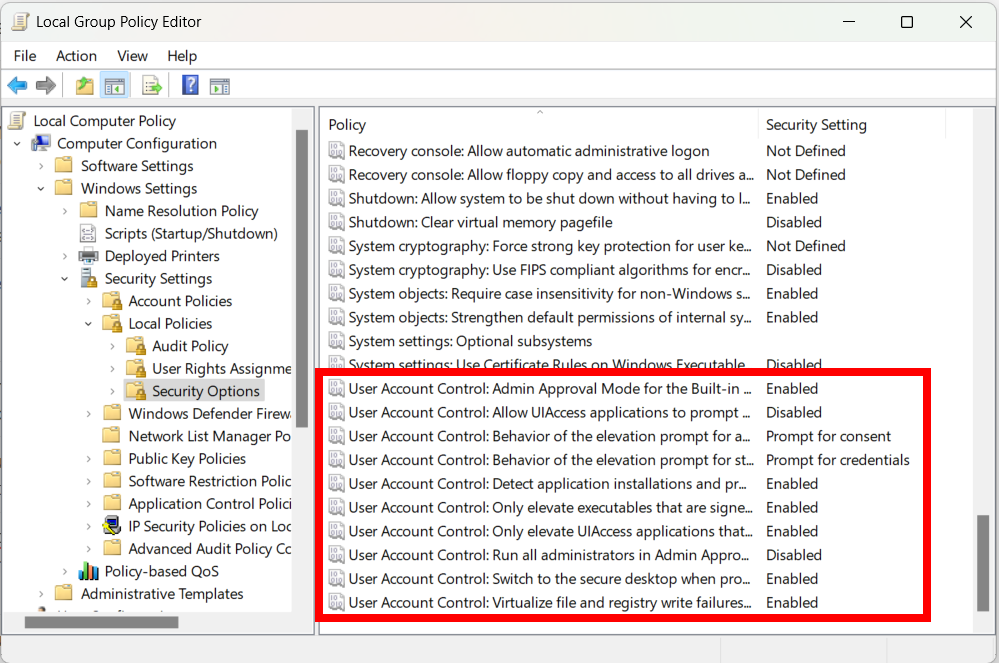
5 User Account Control (UAC)
The UAC is a security feature that prevents users without administrative privileges from changing system settings. When a user wants to perform an action that requires administrator permission, they will receive a prompt asking them to obtain it before proceeding. This ensures that no one can make important changes without the consent of an administrator.
To access the UAC policies in the Group Policy Editor, go to Computer Configuration > Windows Settings > Security Settings > Local Policies > Security Options. Look for policies that start with “User Account Control.”
Here is how you should set it up to make your system more secure:
|
UAC Group Policy |
Setting |
|---|---|
|
Admin Approval Mode for the Built-in Administrator Account |
Enabled |
|
Behavior of the Elevation Prompt for Standard Users |
Prompt for Credentials |
|
Behavior of the Elevation Prompt for Administrators in Admin Approval Mode |
Prompt for Consent |
|
Detect Application Installations and Prompt for Elevation |
Enabled |
|
Only Elevate Executables that are Signed and Validated |
Enabled |
|
Only Elevate UIAccess Applications that are Installed in Secure Locations |
Enabled |
|
Switch to the Secure Desktop When Prompting for Elevation |
Enabled |
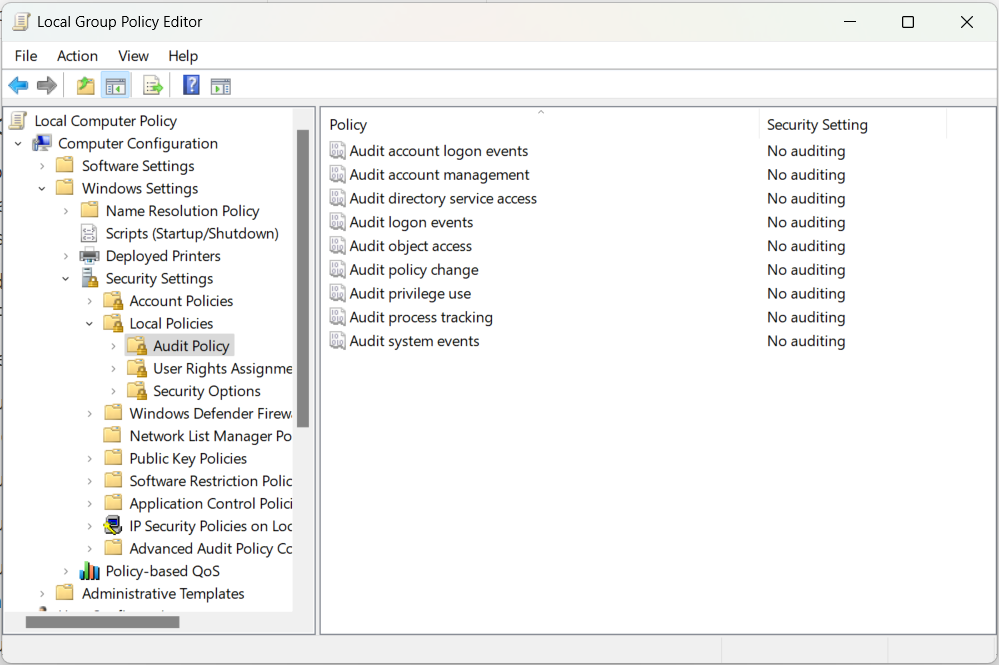
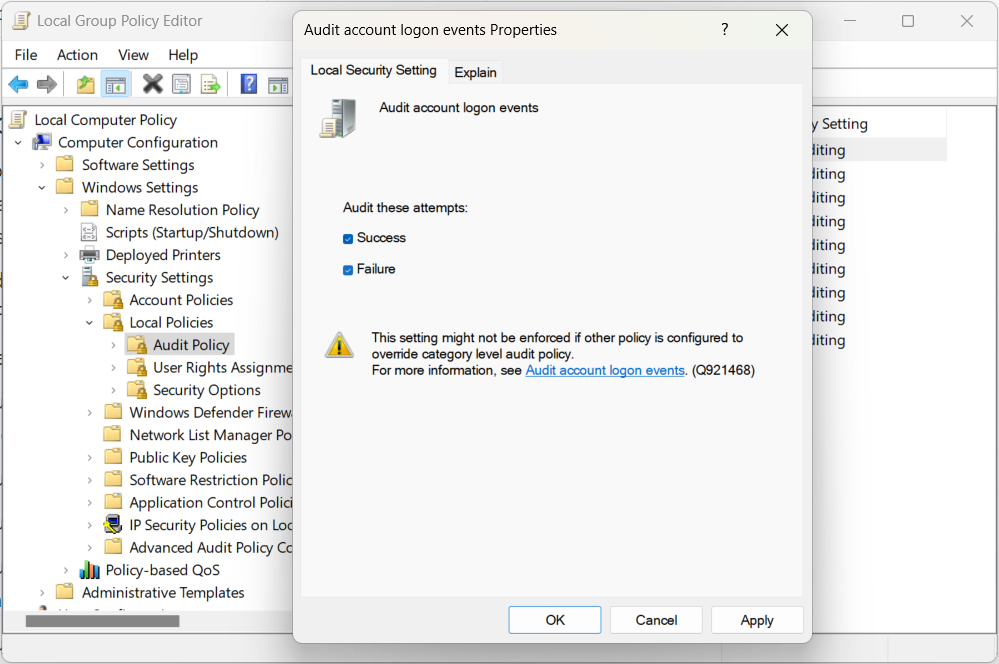
6 Enable Account Audit Policies
Windows allows you to track certain actions regarding user accounts on your system. Reviewing the logs lets you look for suspicious activity, such as failed login attempts, unauthorized access, misuse of elevated privileges, or alterations to account settings.
To find these policies in the Group Policy Editor, go to Computer Configuration > Windows Settings > Security Settings > Local Policies > Audit Policy.
Here, edit the following policies by ticking the “Success” and “Failure” checkboxes:
- Audit account logon events: Track accounts when someone attempts to log in to a specific account.
- Audit account management: Track when someone creates, deletes, or modifies a user account.
- Audit logon events: Track login and log-off attempts on the computer.
- Audit object access: Log instances where a user accesses specific files, folders, and registry entries.
- Audit policy change: Track changes made to group and security policies.
- Audit privilege use: Monitor when a user misuses administrative privileges.
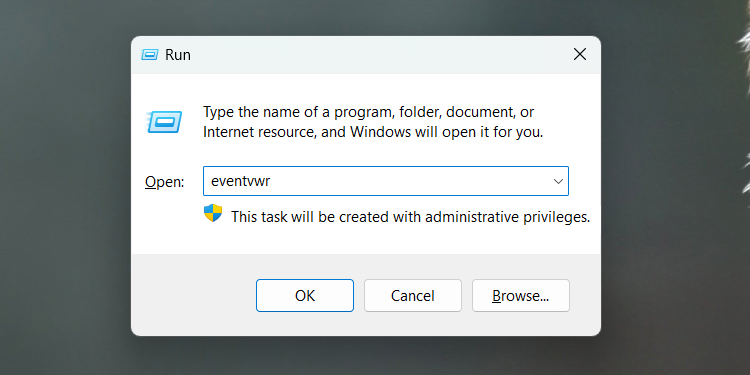
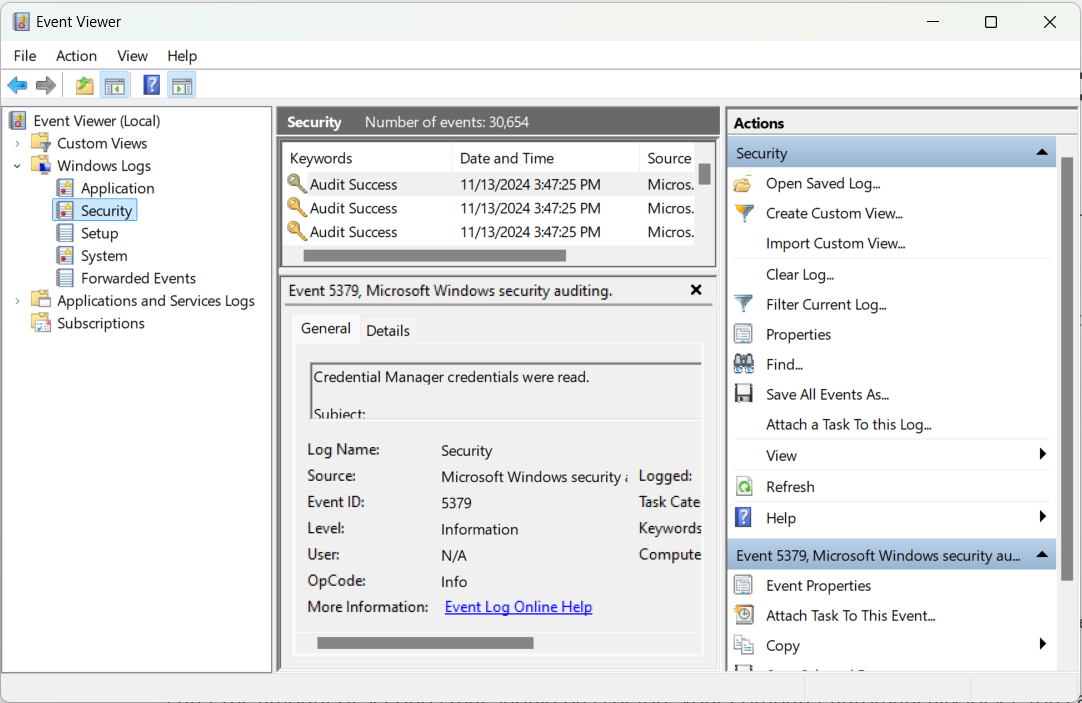
You can find the audit trail of these policies in the Event Viewer. To open it, press Windows+R to bring up Windows Run. Enter eventvwr in the textbox and click the “OK” button.
Then, select Event Viewer > Windows Logs > Security to find the logs created for the audit policies.
Combine these group policy edits along with other Windows Security settings to make your computer as safe as it can be. You can apply these tips whether you’re an IT administrator at a company or someone whose computer is used by others at home.
It’s best to do everything possible to protect your personal data. This includes disabling features like Command Prompt and clipboard history. The safety of your computer is in your hands.