There’s a new family of malware that’s impersonating Asus’s Armoury Crate software and infecting PCs with malicious code.
The malware known as CoffeeLoader may sound like a futuristic kitchen appliance that automatically pours you some morning brew, but its intent is much more nefarious. Once it has infected your PC, it connects to a server to download additional malware in the form of an infostealer, then steals your information and credentials.
Armoury Crate is Asus’s proprietary gaming app for the company’s lineup of gaming PCs. It allows users to control critical aspects of their gaming performance, including their PC’s operating mode, the speeds of fans, and more. Gamers using Asus’s desktop PCs and gaming laptops are at risk of infection, since these are things most gamers will want to do.
The thing that makes CoffeeLoader so gnarly is how well-coded it is to infect gamer PCs. Not only does it mimic Asus’s software, but it also uses a packer called “Armoury” that loads part of its code onto the victim’s GPU (or graphics card). Since all users with Asus gaming PCs have GPUs, they’re vulnerable to this technique. And the fact that it targets a user’s GPU rather than their CPU is also a sneaky way for the malware to evade detection, since most virus scanners don’t typically scan the GPU.
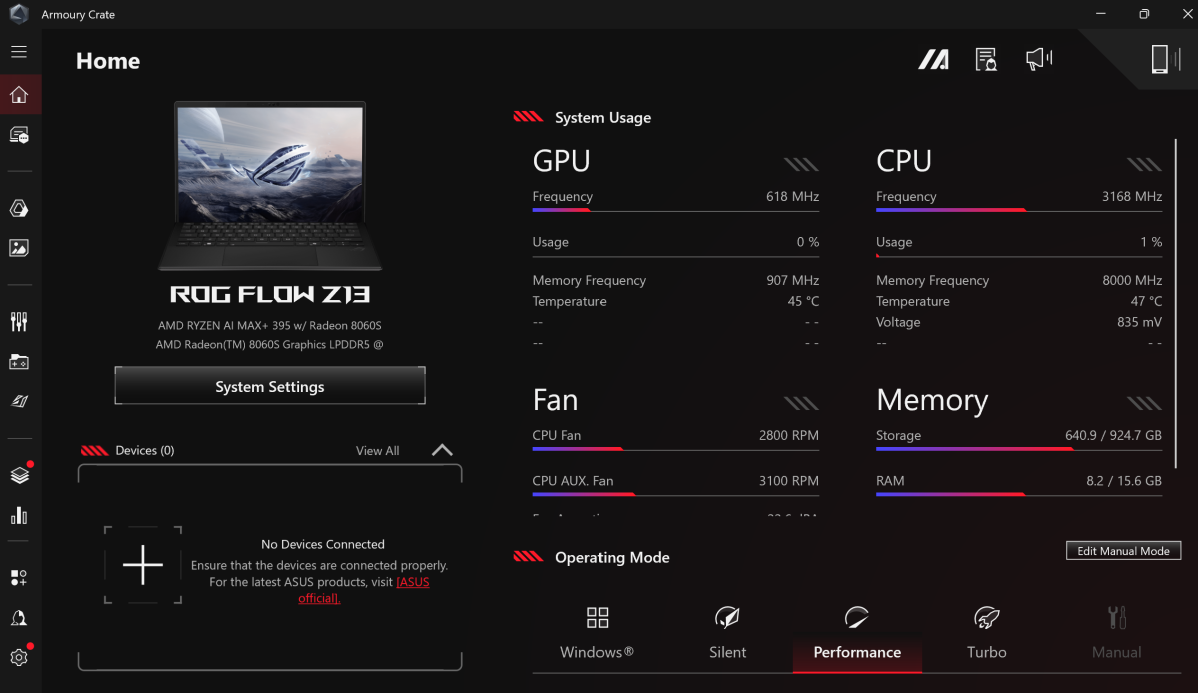
The CoffeeLoader malware mimics Asus’s Armoury Crate app.
Mark Hachman / Foundry
The CoffeeLoader malware also uses other techniques to avoid being discovered by antivirus software. One is called Sleep Obfuscation, whereby it locks itself up in system memory within an inactive, encrypted file that can’t be read. The malware also utilizes unusual pathways to remain unnoticed, such as Windows fibers (which are utilized by a user’s PC when they’re multitasking).
Additionally, CoffeeLoader can carry out Call Stack Spoofing to eradicate traces of itself. Typically, when programs run, they leave traces of code behind like footprints in the snow. But CoffeeLoader is able to change the code it leaves behind just enough to appear like a benign program, thus fooling antivirus programs looking for traces of malicious code.
Zscaler, the cybersecurity firm that discovered the malware, dates CoffeeLoader back to September 2024. With it having technical similarities to another malware called SmokeLoader, they surmise that this could point to CoffeeLoader being a new variant of that malware. But it’s too early to say for sure.
Right now, the best way to avoid infection with CoffeeLoader is to ensure you download Asus’s Armoury Crate software directly from the company’s website rather than any third-party site.




