
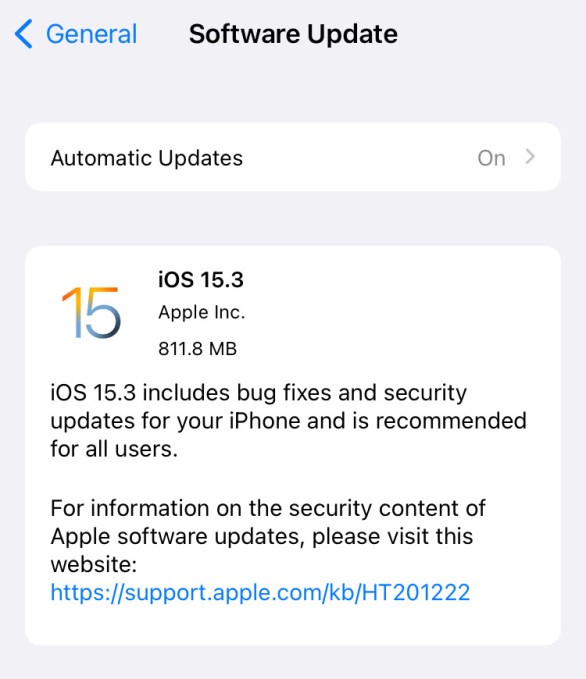
Apple on Wednesday patched dozens of security issues with the release of iOS 15.3 of macOS Monterey 12.2.
IOS 15.3 fixes a total of 10 security bugs, including a flaw that the company says may have been actively exploited. The vulnerability, tracked as CVE-2022-22587, is a memory corruption bug in IOMobileFrameBuffer — a kernel extension that allows developers to control how a device’s memory handles the screen display — that could lead to kernel code execution.
First discovered by FingerprintJS, a browser fingerprinting and fraud detection service, the vulnerability was found in Apple’s implementation of IndexedDB, an application programming interface (API) that stores data on your browser.
The flaw, tracked as CVE-2022-22594, allows any website that uses IndexedDB to access the names of IndexedDB databases generated by other websites during a user’s browsing session, in turn enabling a website to track other websites the user visits in different tabs or windows. In some cases, websites use unique user-specific identifiers in IndexedDB database names, which FingerprintJS warned could allow attackers to access a users’ Google account information.
IOS 15.3 also lands with fixes for security issues that could lead to apps gaining root privileges, the ability to execute arbitrary code with kernel privileges and the ability for apps to access user files through iCloud.
Meanwhile, macOS Monterey 12.2 patches a total of 13 vulnerabilities in total. The latter also promises to bring smoother scrolling to MacBooks, fixing a previously reported scrolling issue in Safari.
Apple also released security fixes for legacy versions of macOS Big Sur and Catalina.
The release of these latest security updates comes just two weeks after Apple released iOS 15.2.2 to fix a vulnerability in iOS and iPadOS that could be exploited via HomeKit to launch persistent denial of service (DoS) attacks.




