Between regular malware, email phishing schemes, scam texts, and data leaks, the digital world feels like a pretty hostile place. CAPTCHAs, a tool that has been used to prevent bots from overwhelming websites with too much traffic, has been impersonated to deliver malware.
How Can a CAPTCHA Install Malware?
Malicious CAPTCHAs themselves can’t directly install malware, but they can exploit how familiar we’ve become to jumping through hoops to get you to install it yourself.
Malicious actors aim to exploit our familiarity with CAPTCHA—instead of a puzzle challenge, they’ll require you to “follow the steps.”
Typically, this involves three things:
- Copy a command to your clipboard (sometimes this is automatic)
- Open up a Run window by pressing Windows+R
- Press Ctrl+V and Enter to execute the command.
If you’re just following CAPTCHA instructions on autopilot (we’ve all been there), you might not question that too much. And, if you’re not familiar with what Windows+R does, you might not spot the danger. Here’s how it works against you.
What Does Windows+R Do, and How Is It Dangerous?
The Windows+R hotkey opens up a Run window. The Run window is a little like a Command Prompt window, except it is much more limited, and it isn’t interactive. However, you can launch programs from it, and you can also pass commands to those programs. Malicious actors have their unsuspecting victims copy a small script to the Run window. That script will usually download malware from the internet using PowerShell and a few native Windows applications.
If you want to see how this sort of thing could work for yourself, I’ve included a harmless example that will just open up the System Information window. Press Windows+R, then paste the following line in and press Enter:
powershell -Command "start msinfo32"
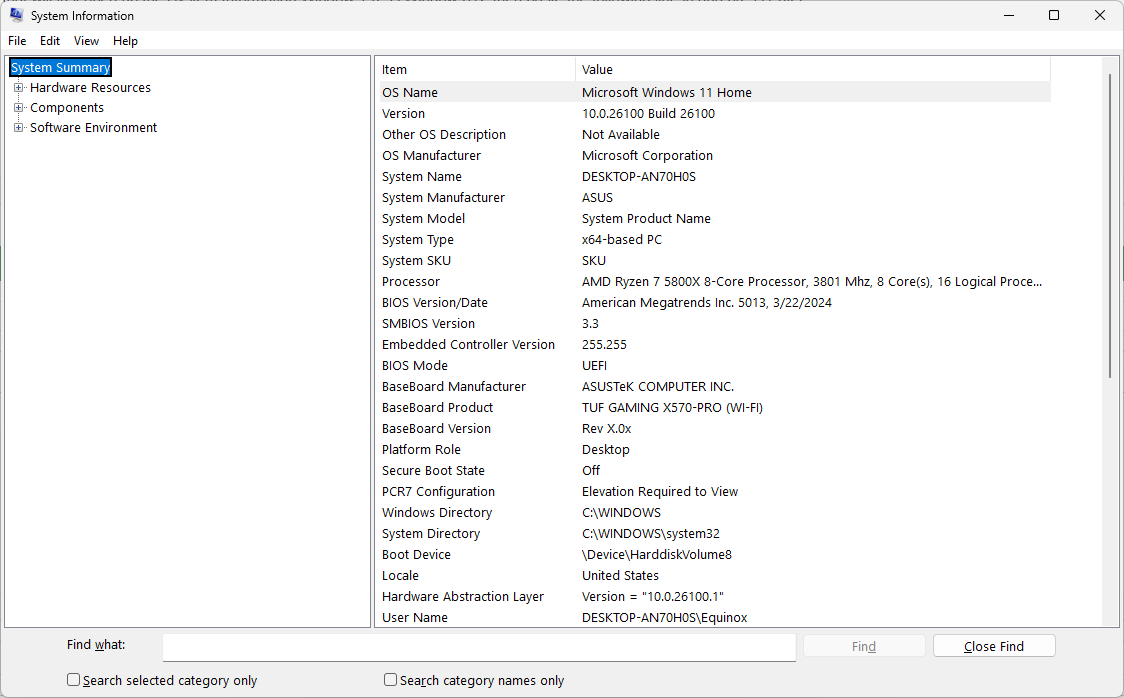
You’ll see something like this pop up:
The exact same method can be used to download malware, execute malicious scripts, or otherwise make your life more difficult. To make matters worse, the malicious command is usually obfuscated, so you can’t immediately tell what it did just by reading it.
How You Can Protect Yourself
As the saying goes, an ounce of prevention is worth a pound of cure. If a CAPTCHA tries to get you to run a script, don’t. There is never any reason for a CAPTCHA to have you execute anything on your PC.
There is also never a reason for a CAPTCHA to have you open up a utility on your PC and type commands. If one asks you to do that, you should leave the website—it has likely been compromised with malware.
Similarly, a CAPTCHA should never ask you to download or install anything.
CAPTCHAs, after all, are basically puzzles designed to weed out AI from humans. They can fulfill that purpose without installing something.
What Should You Do If You Ran the Command?
If you do wind up running a command from a malicious CAPTCHA, the first thing you should do is disconnect your PC from the Internet, at least until you get a better idea of what is going on. Not all malware needs or can use an internet connection, but some of the most dangerous malware can.
If you logged in to any important websites after you ran the script, like your bank, you should use another device to change the passwords for those sites immediately, and enable two-factor authentication, if you haven’t already.
Now you have a choice: you can completely reset your PC, which is very likely to eliminate any malware, or you can attempt to clean up your PC.
Microsoft has made resetting your PC extremely easy. Press Windows+I to open the Settings app, navigate to System > Recovery > Reset This PC, and select the “Keep My Files” option. You could choose the option to wipe everything, but it probably isn’t necessary.

What’s the Best Way to Back Up My Computer?
A little bit of preparation now will save you a massive headache later.
How to Clean Up Your PC
If you choose to try and clean up your PC, there are about a handful of steps you need to take.
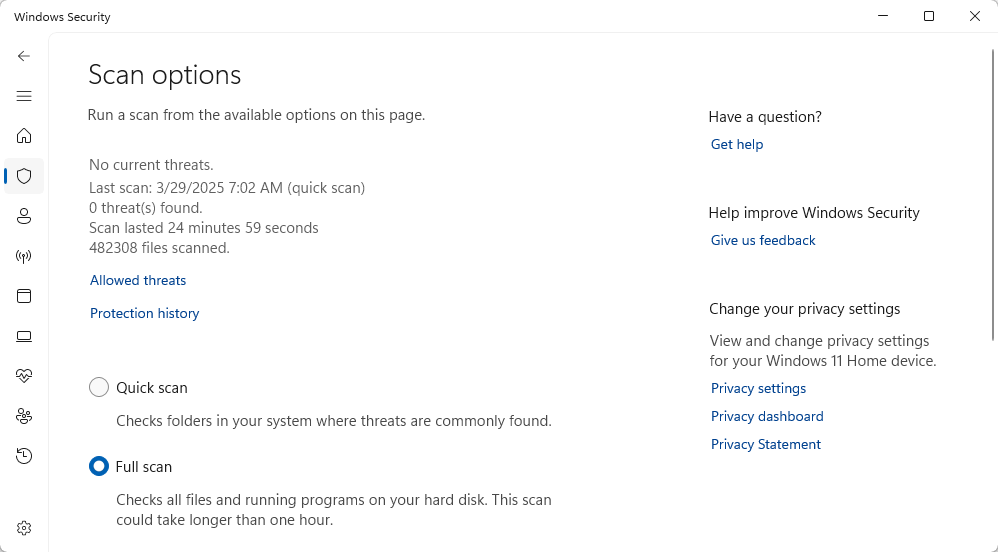
First, use Windows Security to run a full system scan. It may not pick up everything, but it is a great first step.
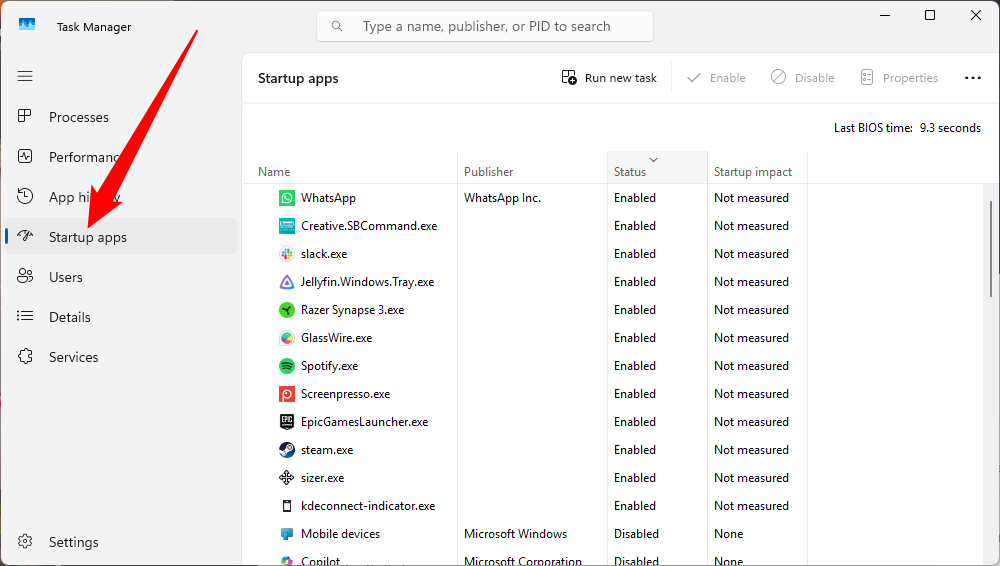
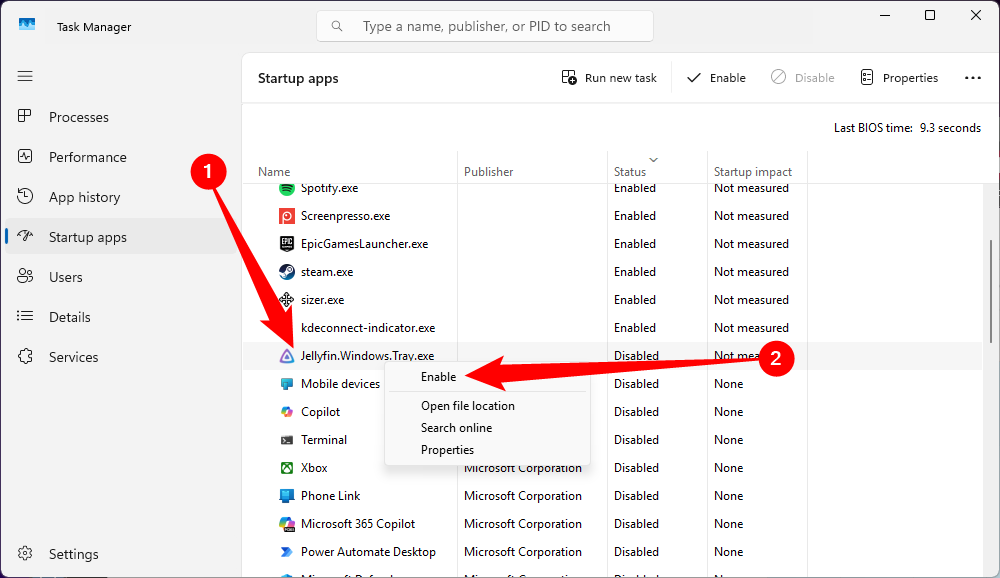
While Windows Defender is doing that, press Ctrl+Shift+Esc, then click the “Startup Apps” tab. Sometimes malware will add itself to the startup list so that it runs whenever you turn on your PC.
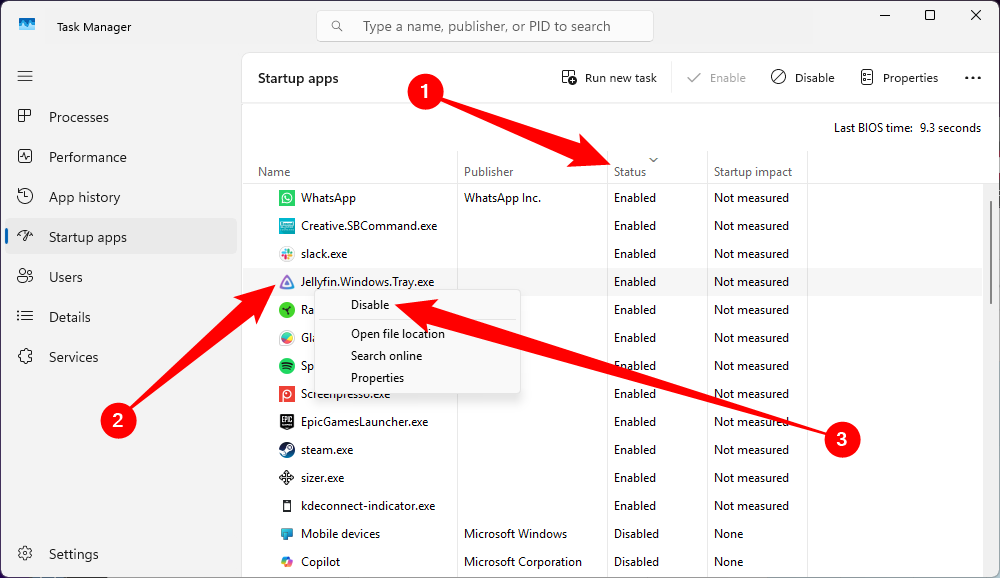
Click the “Status” header until you have your startup applications sorted so that the enabled apps are listed first, then scroll through them carefully. You can safely ignore any app that has Microsoft Windows, Microsoft Corporation, or Microsoft in the Publisher tab. However, if you see something you don’t recognize or that strikes you as suspicious, right-click it and hit “Disable.”
There is no way for you to break your PC with this menu—at worst, you might disable something you actually use, but you can always come back and enable it if you need it.
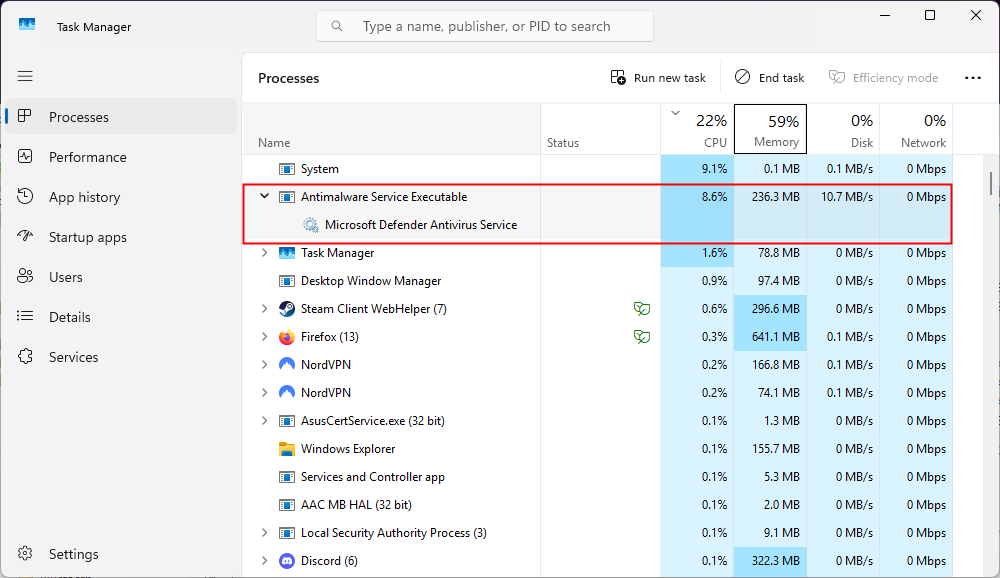
While you have the Task Manager open, head over to the “Processes” tab and look for any applications you don’t recognize that are using up a lot of resources. You should expect Antimalware Service Executable to be using up a lot of resources—that is the Windows Security scan running.
However, beyond that, look for anything you don’t recognize. If you spot something you aren’t familiar with, the quickest way to determine if it is malware is to search the internet on a different device. Microsoft’s applications and services are extensively documented, and you’ll likely get plenty of hits for legitimate programs too. However, if you find nothing about an application, that is a pretty serious red flag.
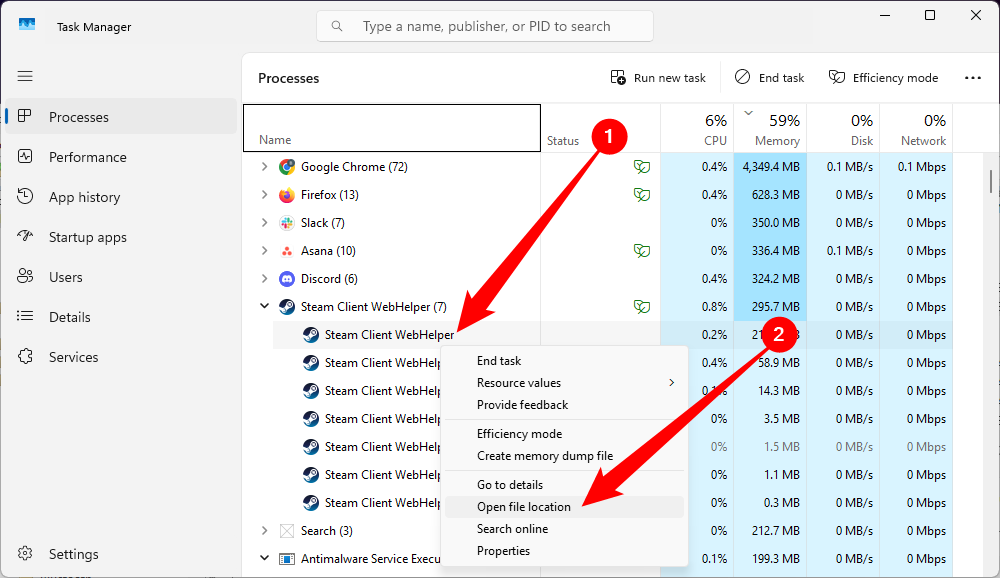
Once you find something suspicious, right-click it and select “Show File Location.”
If you want to go the extra mile, then you could also check Task Scheduler, though I wouldn’t recommend it unless you’re familiar with the software on your PC. Some malware will create a task that will periodically redownload itself, which could leave you playing whack-a-mole. Unfortunately, checking through Task Scheduler is really tedious.
There are an enormous number of tasks on most PCs, and it isn’t always obvious what something actually does. If you’re unfamiliar with which applications perform which functions, you’ll have to look these tasks up on the internet one by one.
In general, you can be pretty sure that anything in “C:\Microsoft” isn’t malware. However, if you find a random executable that was created at the same time as you ran the script from the CAPTCHA, you should delete it.
Once the Windows Security scan is complete, and you’ve checked the Task Manager and your startup apps for anything suspicious, you can be reasonably sure you’re malware-free. At this time, feel free to reconnect to the internet. As a final precaution, I’d recommend downloading and installing Malwarebytes and then running a virus scan with it.
It is important to note that there are no guarantees when it comes to cybersecurity—new exploits are created, discovered, and used every single day, and there is no way to be completely sure your scans have found and removed all malware.